Security at the core!
At Panto, we treat your data with the utmost care. Our security framework combines advanced encryption, stringent access protocols, and proactive monitoring to ensure your information is always protected.
Have Questions?Our security team is ready to assist. Reach out anytime at security@getpanto.ai— we prioritize clear, prompt responses to keep you informed.
Transparency Builds Trust
Trust is at the heart of every strong relationship, and we believe transparency is its foundation. That's why we've crafted this document with simplicity and clarity, avoiding unnecessary jargon. Our goal is to make it easy for you to understand how we operate so you can feel confident in trusting us with your business.
Integration Approaches
Cloud Hosted
- Panto's infrastructure is hosted on Microsoft Azure. For details on Azure's security measures, visit the Azure Trust Center.
- To learn about Azure's compliance certifications, including SOC reports and ISO standards, visit the Azure Compliance page.
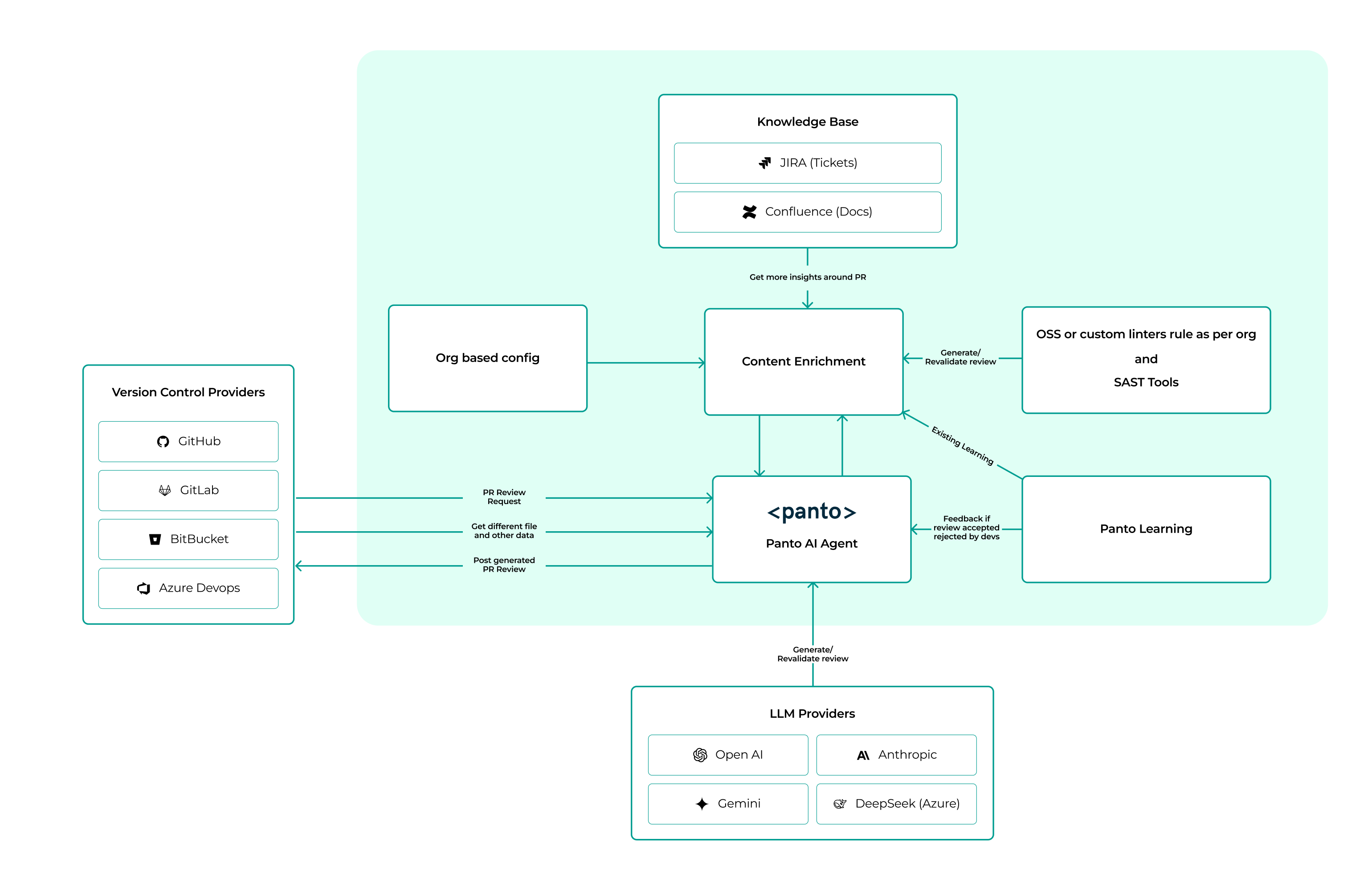
- Panto leverages multiple AI Interfaces to deliver code reviews:
- OpenAI: For AI inference via OpenAI's Enterprise API. Learn more about their security practices on the OpenAI Enterprise Privacy page.
- Anthropic: For AI inference via Anthropic's API. Details about their security practices are available on the Anthropic Commercial Terms page.
- DeepSeek: Accessed through Azure AI Foundry for secure and scalable AI capabilities. Learn more on the DeepSeek Azure Policy.
- Google Gemini: Integrated directly for advanced AI inference. Explore their security practices on the Google Gemini Security page.
Self Hosted/On-Premise
For self-hosted Panto services, custom applications are hosted on your own infrastructure—whether on-premises or in your virtual private cloud (VPC). This allows you and your users to build, run, and use Panto securely behind your virtual private network (VPN).
Bring your own Cloud-BYOC
With Panto, you can bring your own cloud. Our self-hosted solution is designed to integrate seamlessly with your chosen cloud environment, ensuring flexibility and control over your data and infrastructure.
Bring your own Large Language Model (LLM) Inference - BYOLLM
Customers who choose to self-host Panto can also opt to self-host their LLMs instead of relying on third-party APIs. Additionally, Panto supports a “bring your own LLM” model, allowing you to integrate your own LLM by providing a base URL and API keys.
Storage of Customer Code
Panto does not store customer code. The actual code is retrieved on an 'as needed' basis from the customer's version control system, such as GitHub, GitLab, BitBucket, AzureDevOps and is only used for the duration of the processing task, typically lasting a few minutes, but is never stored.
For customers who opt for the on-premises deployment option, their code remains entirely within their own servers or provisioned cloud environment. In this case, no code or related data leaves the customer's infrastructure at any point, ensuring maximum control and security over their intellectual property.
Storage of Customer Metadata
Panto stores customer metadata for analytics and reporting purposes. This metadata includes information such as the number of pull requests opened or closed, comments provided by Panto, information of comments accepted or rejected by developers, and similar activity-related data. Additionally, Panto stores comments generated by the system to enable the bot to learn and improve over time, ensuring a higher signal-to-noise ratio in its outputs.
All metadata is stored securely and is used solely to enhance the functionality and performance of the service. For customers using the on-premises deployment option, all metadata remains within the customer's own infrastructure, ensuring full control and compliance with their security policies.
Confidentiality
At Panto, we enforce strict controls over employee access to customer data. While some employees require access to systems that store or process this information to operate and support Panto services, such access is limited and closely monitored.
For instance, if you encounter an issue with Panto, our team may need to access your account to diagnose and resolve the problem. However, employees are prohibited from viewing customer data unless absolutely necessary. To ensure accountability, we implement technical controls and audit policies that log all access to customer accounts.
Every Panto employee and contractor is bound by our confidentiality policies, which we uphold as a top priority. Protecting your data is not just a policy—it's a core value.
Our Team's Commitment to Security
At Panto, we ensure that every employee undergoes a thorough background check before joining the team. During onboarding and throughout their tenure, employees receive regular privacy and security training to stay updated on best practices and emerging threats.
Every team member is required to review and sign our comprehensive information security policy, which outlines our commitment to the security, availability, and confidentiality of Panto's services.
If you have any questions about our personnel practices or security measures, feel free to reach out to security@getpanto.ai, and we'll respond promptly.
Return and Deletion of Customer Data
At Panto, we respect your control over your data. If your contract with us ends, you can request the return of any customer data stored by Panto by dropping a mail on hello@getpanto.ai.
Once initiated, we ensure a hard delete of your data from our production systems within 48 business hours.
Certifications and Audits
Panto is committed to maintaining the highest standards of security and compliance. We have undergone a Secure Code Review Audit conducted by a certified CERT-IN, empanelled auditor. This audit ensures that our codebase adheres to stringent security practices, minimizing vulnerabilities and safeguarding your data.
Customers can request a copy of our Secure Code Review Audit Report by reaching out to security@getpanto.ai.
Architecture Diagram